Your Microsoft 365 tenant can leak data silently - no malware, no alerts. Learn how simple misconfigurations enable ongoing email and data exfiltration.
 Your Microsoft 365 Tenant Has a Silent Data Leak. It Requires No Malware.
Your Microsoft 365 Tenant Has a Silent Data Leak. It Requires No Malware.
Your Microsoft 365 tenant can leak data silently - no malware, no alerts. Learn how simple misconfigurations enable ongoing email and data exfiltration.
 Security Alerts That Nobody Investigates - And Why That’s More Dangerous Than Having None
Security Alerts That Nobody Investigates - And Why That’s More Dangerous Than Having None
Security alerts mean nothing if no one investigates them. Ignored alerts create false confidence - and give attackers the time they need to cause real damage.
 The Silent M365 Risk Most CXOs Discover Too Late: External Access That Never Expired
The Silent M365 Risk Most CXOs Discover Too Late: External Access That Never Expired
A hidden Microsoft 365 risk many CXOs overlook - expired external access that quietly breaks Zero Trust and exposes organizations to serious security gaps.
 The Shadow Admin Problem in Microsoft 365 – A Silent Risk Most CXOs Miss
The Shadow Admin Problem in Microsoft 365 – A Silent Risk Most CXOs Miss
Shadow admins in Microsoft 365 create invisible security, compliance, and governance risks - often without CXOs realizing how exposed their environment truly is.
 Your Defender Is On. So Why Is CEO Impersonation Still Working?
Your Defender Is On. So Why Is CEO Impersonation Still Working?
Defender being “on” isn’t enough. Why CEO impersonation still works in Microsoft 365 - and how misconfigured trust exposes organizations to fraud.
 The Most Dangerous Permission in SharePoint Is Hiding in Plain Sight
The Most Dangerous Permission in SharePoint Is Hiding in Plain Sight
A hidden SharePoint permission - “Everyone Except External Users” - quietly breaks Zero Trust, exposing internal data and amplifying risk in the age of Copilot.
 Your Shared Mailbox Is Quietly Breaking Zero Trust - And Most Organizations Don’t See It
Your Shared Mailbox Is Quietly Breaking Zero Trust - And Most Organizations Don’t See It
Shared mailboxes often bypass Zero Trust controls - creating silent security gaps. Here’s how excessive access quietly puts organizations at risk.
 Microsoft Security Tools Already Exist - They’re Just Barely Being Used
Microsoft Security Tools Already Exist - They’re Just Barely Being Used
Your Microsoft security stack is already there - but misconfigured, underused, and leaving real risk exposed. Licenses don’t equal protection.
 How to Block USB Devices and Protect Corporate Data
How to Block USB Devices and Protect Corporate Data
Learn how to block USB devices in Microsoft 365 using Intune and Defender to stop data theft, malware, and unauthorized file transfers.
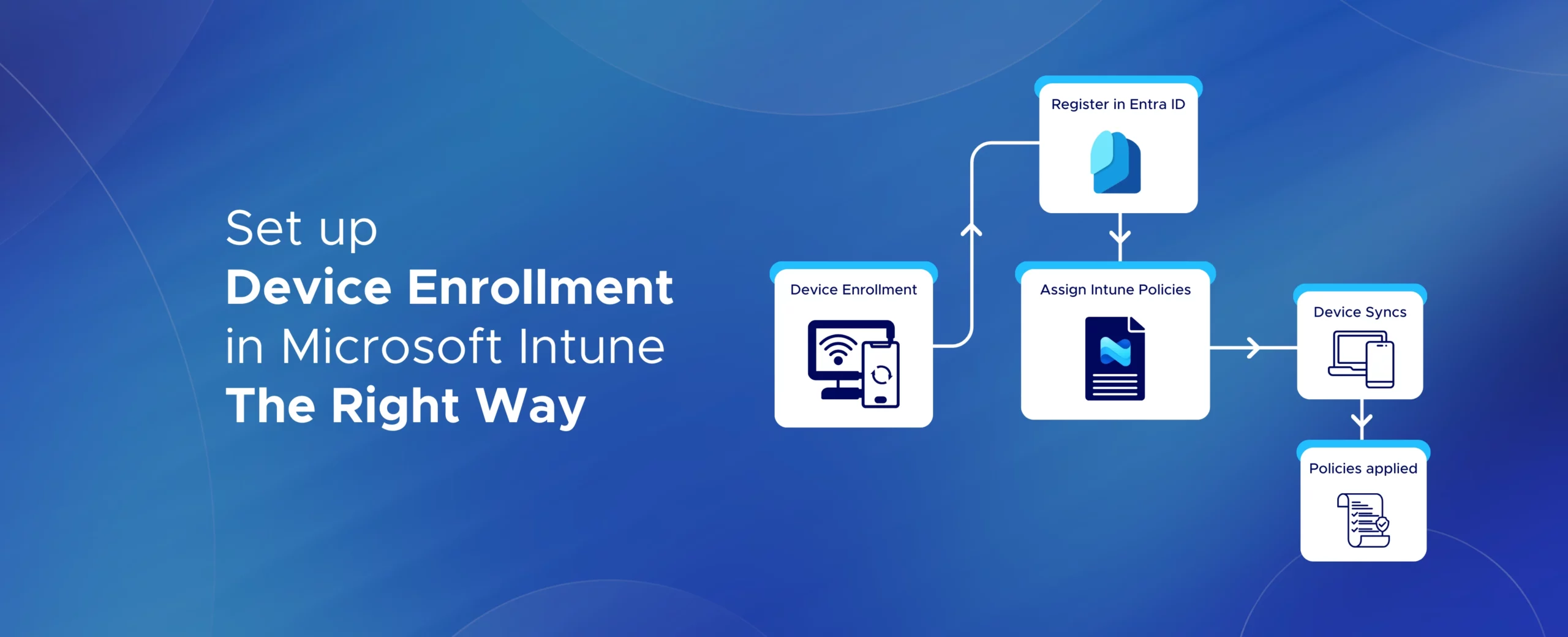 Set Up Device Enrollment in Microsoft Intune – The Right Way - 2026 Guide
Set Up Device Enrollment in Microsoft Intune – The Right Way - 2026 Guide
Learn how to set up Microsoft Intune device enrollment, choose the right method for Windows, iOS, Android, and macOS, and avoid common setup mistakes.