Learn how to set up Microsoft Intune device enrollment, choose the right method for Windows, iOS, Android, and macOS, and avoid common setup mistakes.

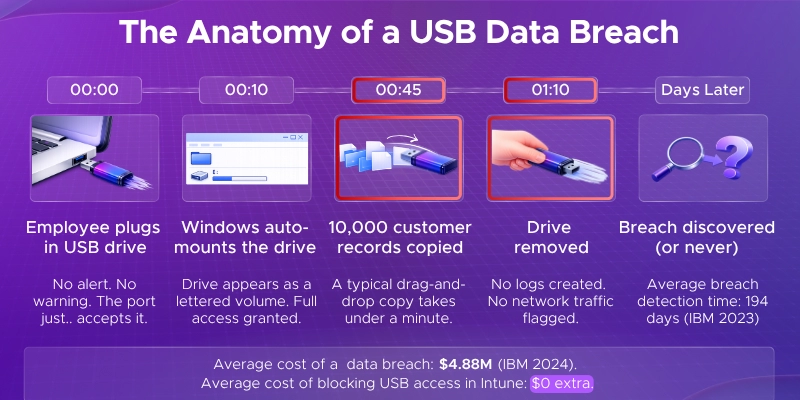
Imagine this: an employee plugs in a USB drive, copies 10,000 customer records, and walks out the door.
No alarms. No warnings. No way to stop it - because no policy was in place.
USB drives are handy. They're also one of the easiest ways for data to walk right out of your building.
A single unprotected USB port can let an employee copy thousands of files in seconds - or let malware silently enter your network. That's a problem no business can afford to ignore.
The good news? If you're using Microsoft 365, you already have powerful tools to fix this.
Microsoft Intune and Defender for Endpoint give IT teams full control over USB access - without needing expensive third-party software.
Here's exactly what this guide covers:
USB drives are so common that most people don't think twice about using them.
That's exactly what makes them dangerous.
A small flash drive can hold gigabytes of sensitive data - customer records, financial reports, trade secrets - and move it all in under a minute. No network connection needed. No logs. No trace.
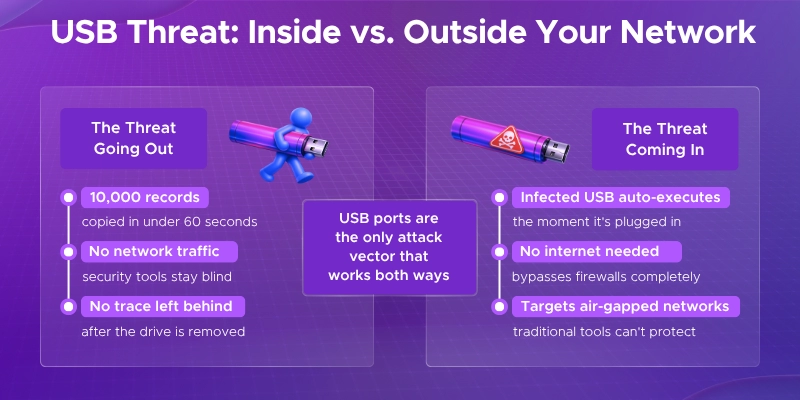
Employees - whether malicious or just careless - can copy confidential files onto a personal USB drive and walk out with them.
This is one of the most common causes of insider data leaks, and it's incredibly hard to detect after the fact.
USB drives don't just take data out - they can bring threats in.
A famous example is Stuxnet, a powerful piece of malware that spread through USB drives and caused real-world damage to industrial systems. It's a clear reminder that a single infected drive can bypass your entire network security.
Most organizations have no idea what's being copied to USB drives.
Without proper controls, there's no way to track who plugged in what, when, or what files were transferred - making USB ports a blind spot in your security setup.
If your organization handles sensitive data, uncontrolled USB access isn't just a security problem - it's a legal one.
Regulations like GDPR, HIPAA, and PCI DSS all require strict control over how data is accessed and moved. Failing to restrict removable storage access can put you in direct violation of these standards.
The numbers back this up:
Before diving in, make sure you have the following in place:
Licensing
Admin Access
Device Requirements
Pre-Planning
There's no single way to block USB devices in Microsoft 365 - the right method depends on your license, environment, and how much control you need.
Use Case: You want to completely block all USB removable storage for all users, with no exceptions. This is the simplest and quickest option.
Prerequisites
Steps
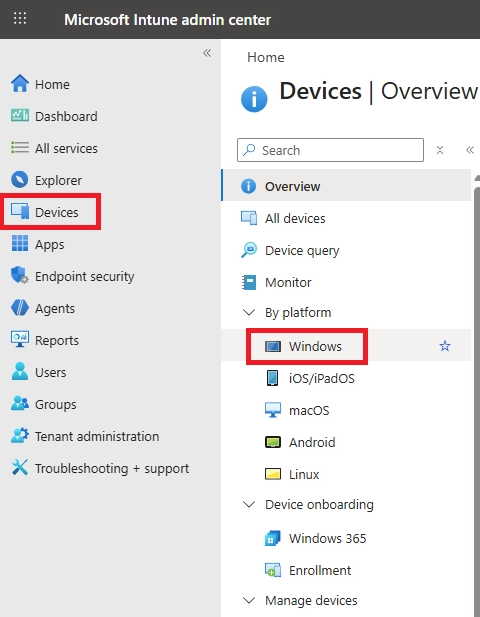
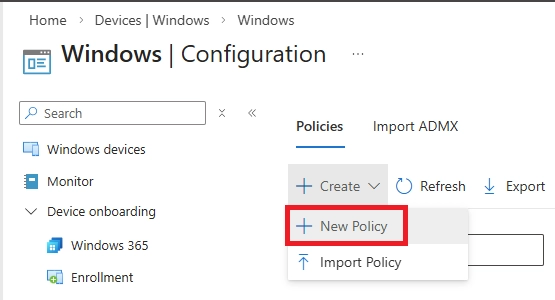
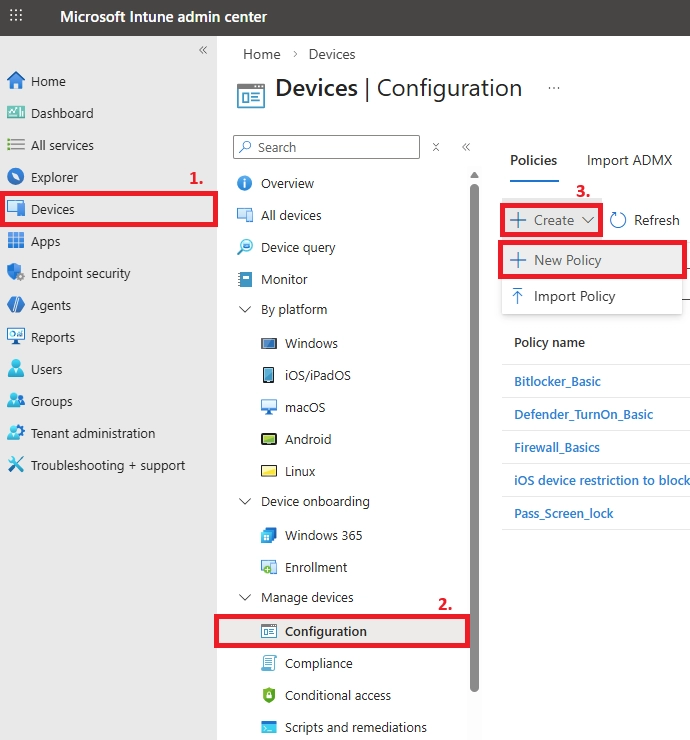
Step 1: Sign in to the Intune admin center, go to https://intune.microsoft.com
Step 2: Navigate to Device Configuration
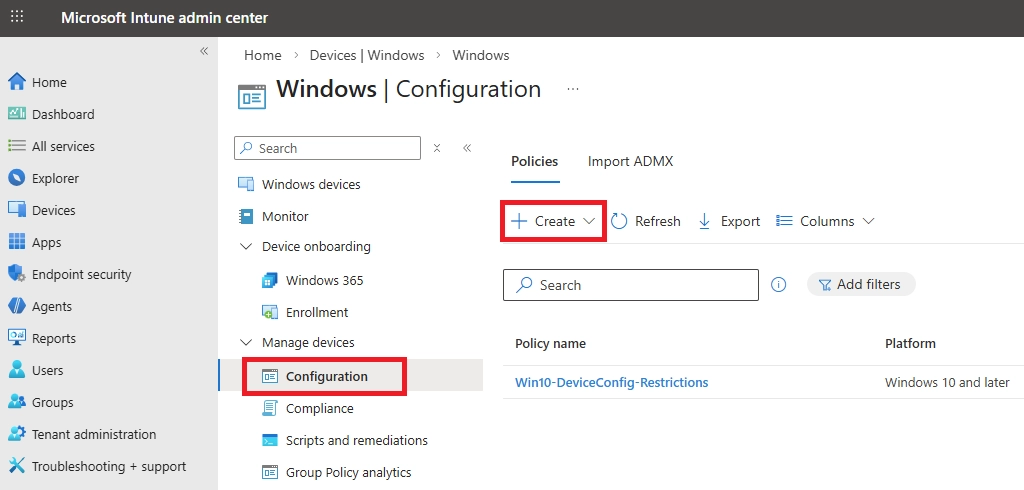
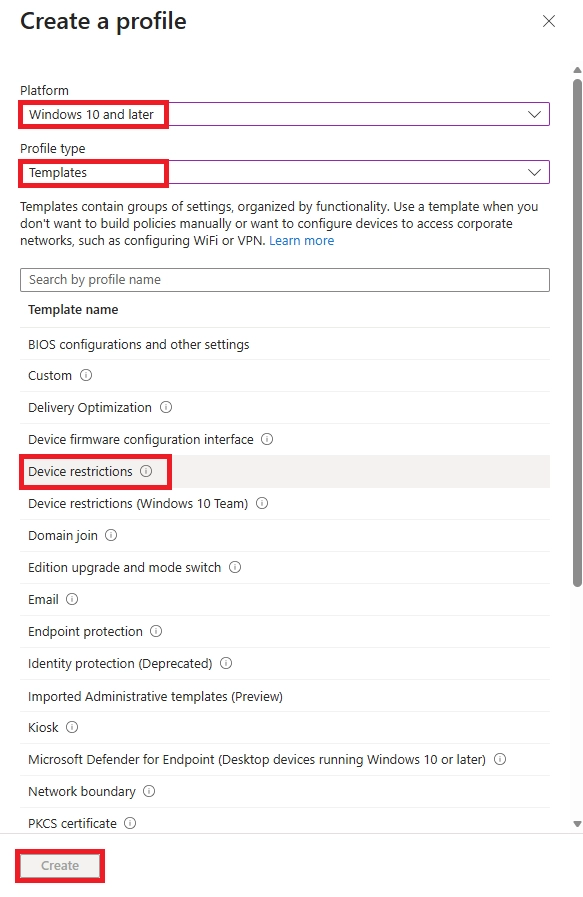
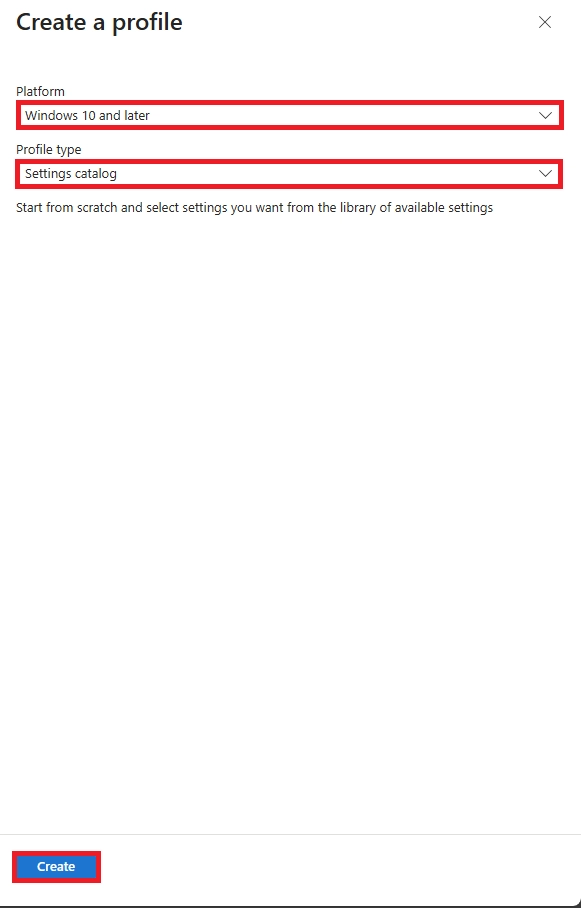
Step 3: Set platform and profile type
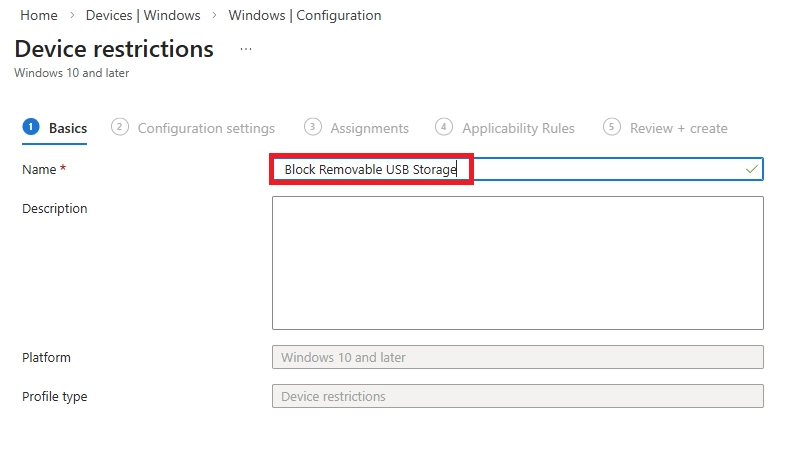
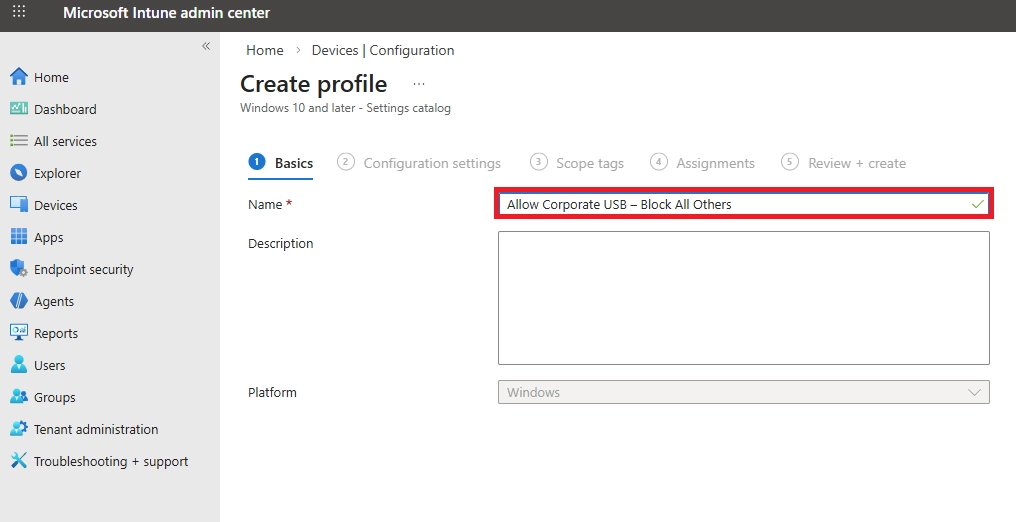
Step 4: Fill in Basics
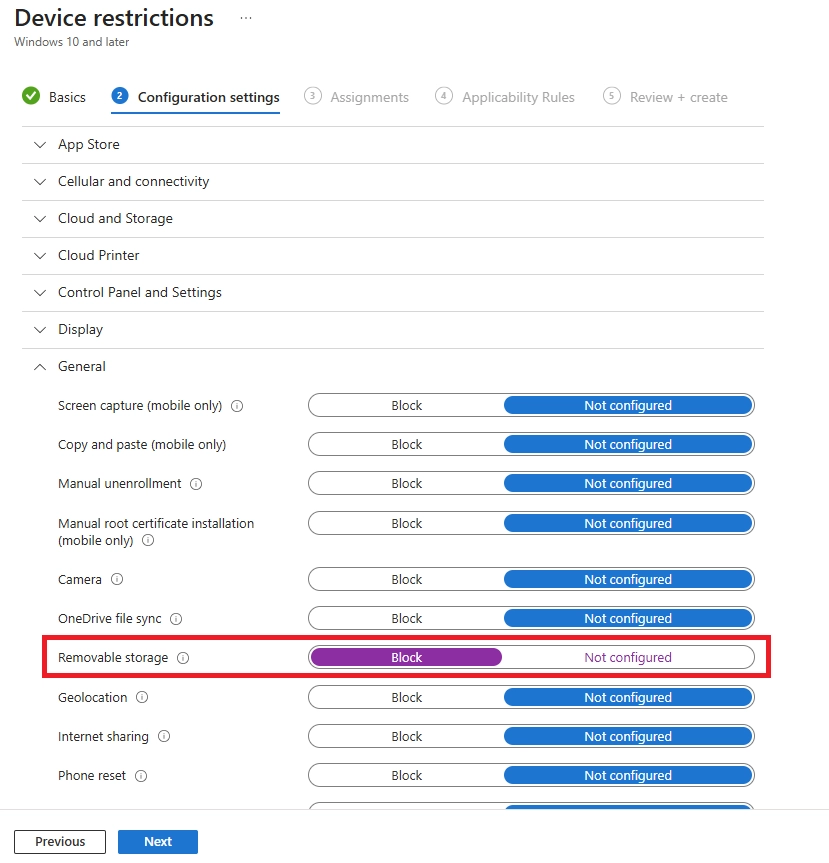
Step 5: Configure the setting
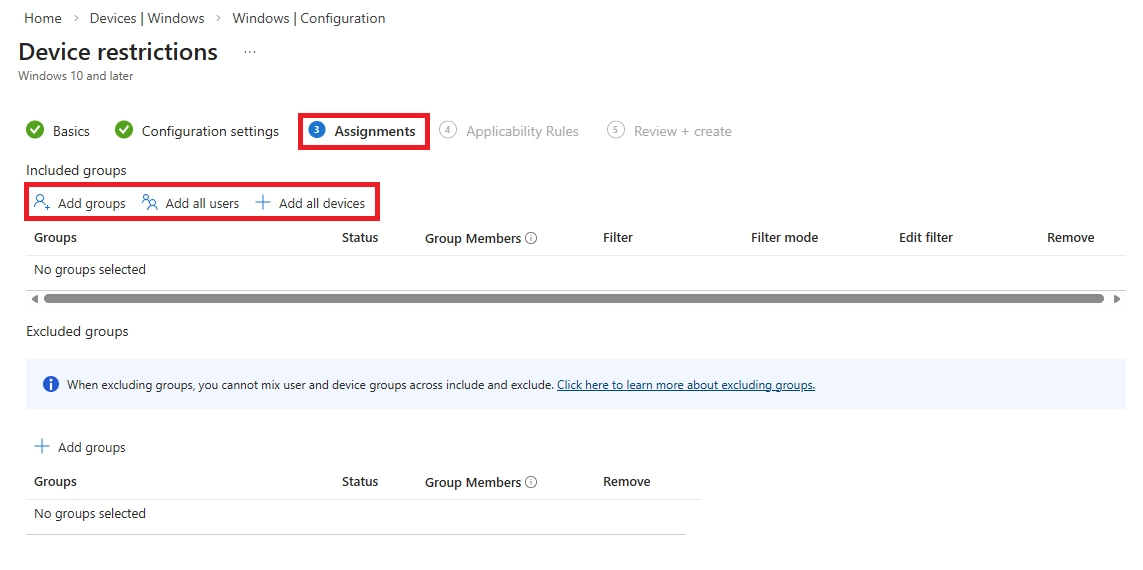
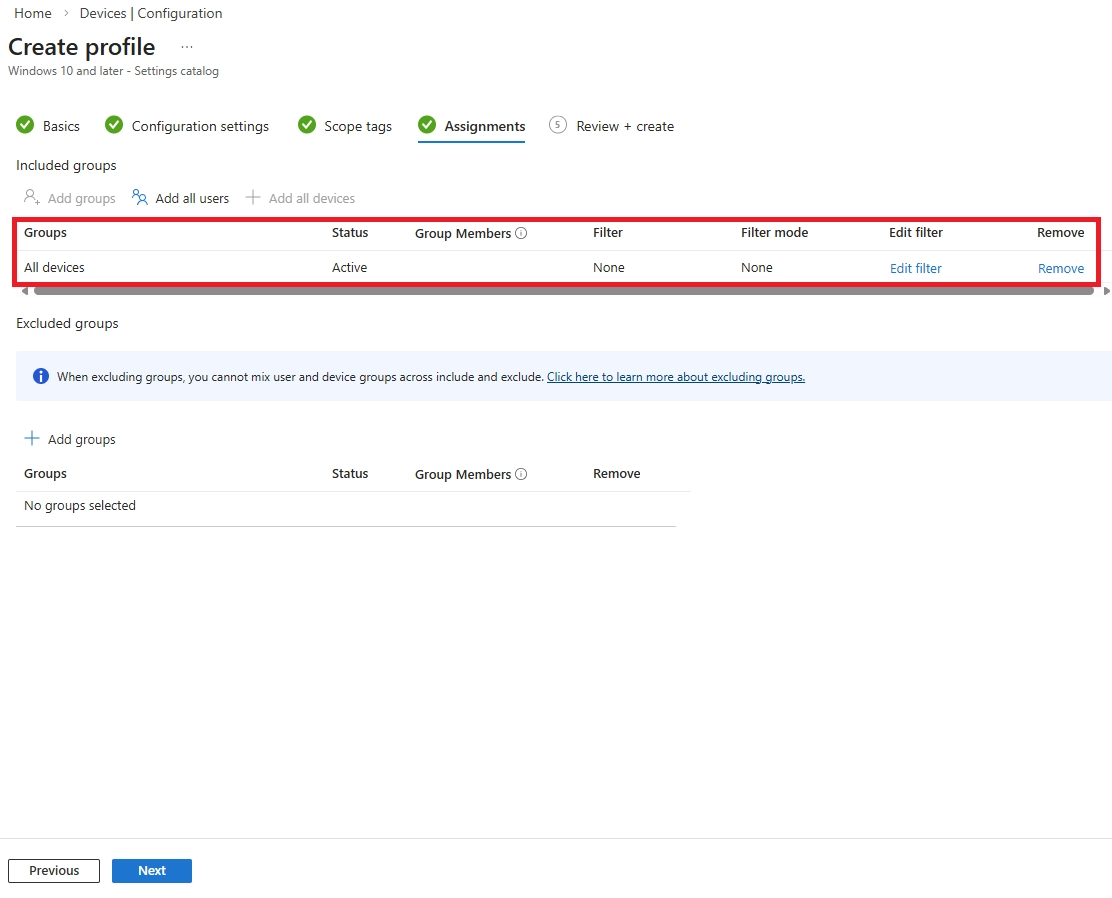
Step 6: Assign the policy
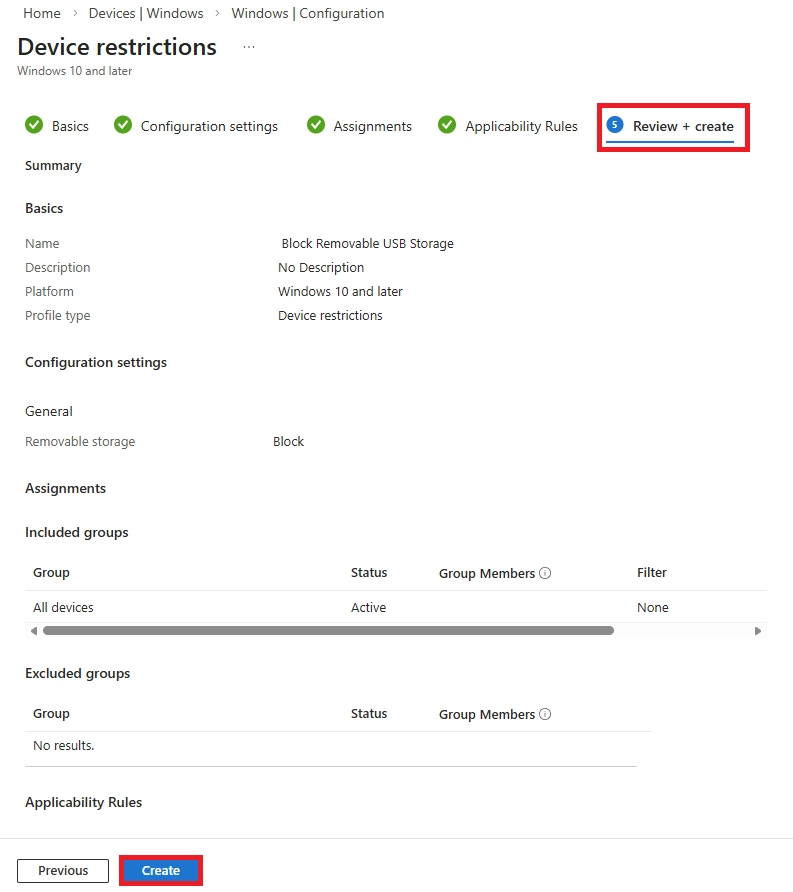
Step 7: Review and create
When a USB drive is connected and accessed on a policy-managed device, Windows immediately throws this error - D:\ is not accessible, Access is denied - confirming the Intune Device Restrictions policy is actively enforced.
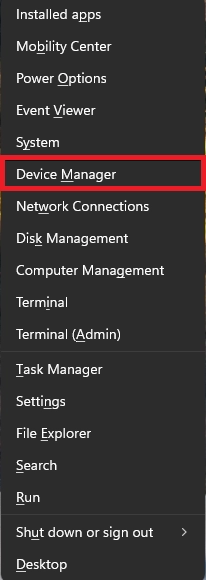
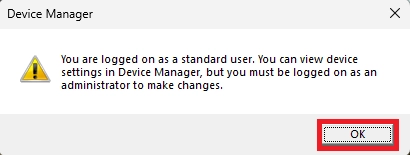
Do this on any Windows machine first:
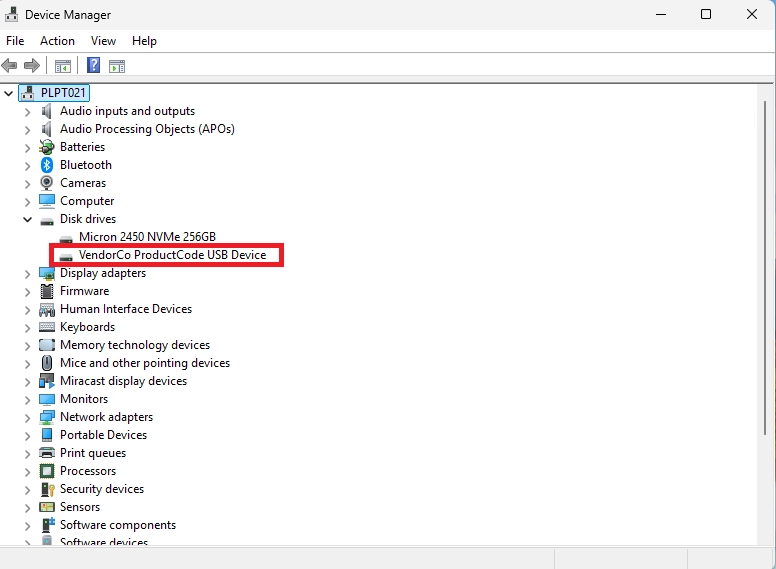

USBSTOR\DiskSanDisk_Ultra________1.00
USBSTOR\DiskSanDisk_Ultra________
USBSTOR\DiskSanDisk_Ultra
USBSTOR\GenDisk
Now go to Intune:
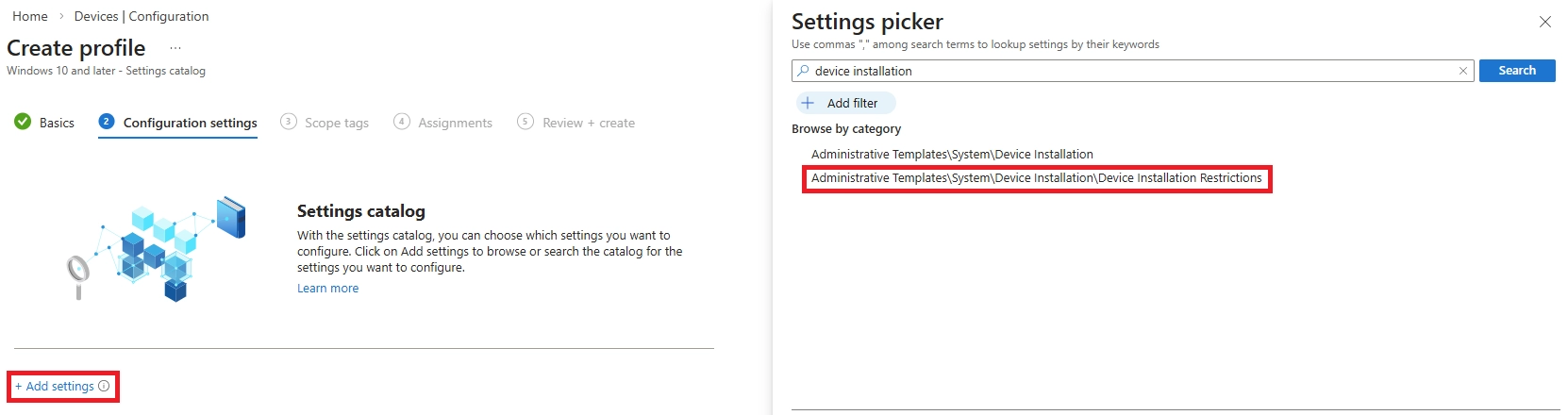
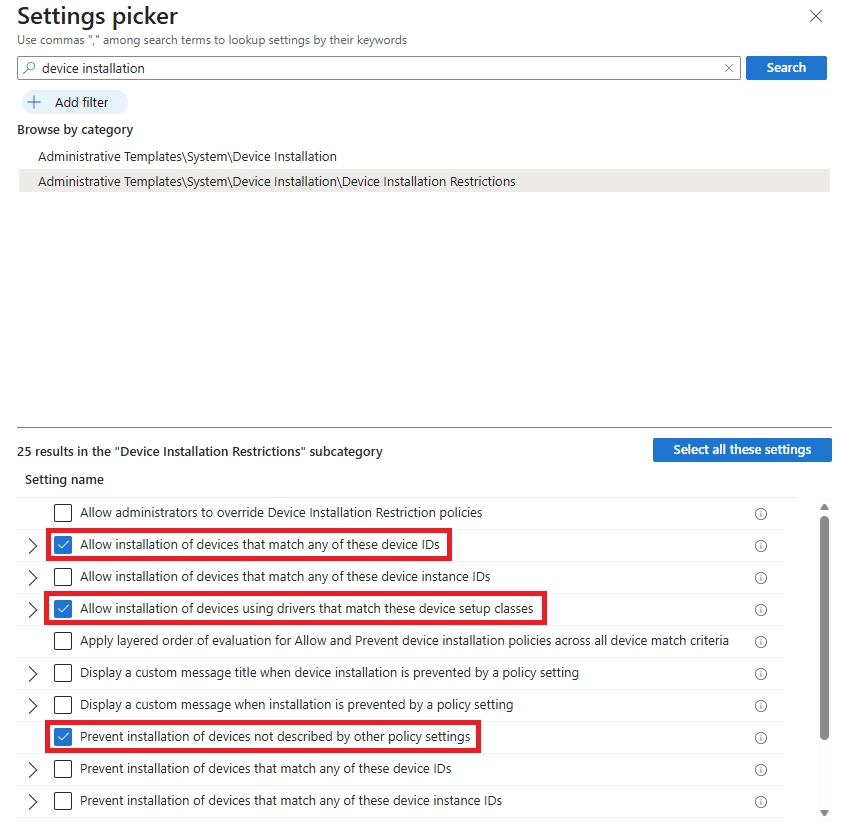
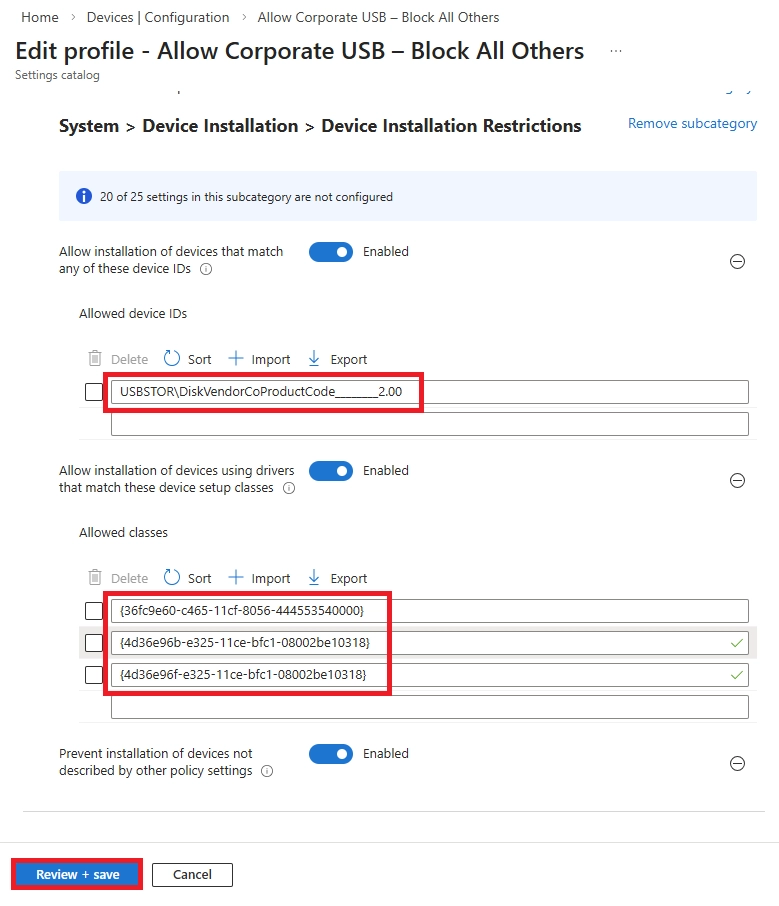
Setting 1 - Prevent installation of devices not described by other policy settings
Setting 2 - Allow installation of devices that match any of these Device IDs
USBSTOR\DiskSanDisk_Ultra________1.00
USBSTOR\DiskKingston_DataTraveler_G2
Setting 3 - Allow installation of devices using drivers that match these device setup classes
{36fc9e60-c465-11cf-8056-444553540000} → USB controllers (MANDATORY)
{4d36e96b-e325-11ce-bfc1-08002be10318} → Keyboard
{4d36e96f-e325-11ce-bfc1-08002be10318} → Mouse
{4d36e979-e325-11ce-bfc1-08002be10318} → Printer

A system notification further reinforces the block, displaying the message - 'The installation of this device is forbidden by system policy. Contact your system administrator' - confirming that the Intune Device Control policy is actively enforced and no unauthorized USB device can be installed or accessed on this endpoint."
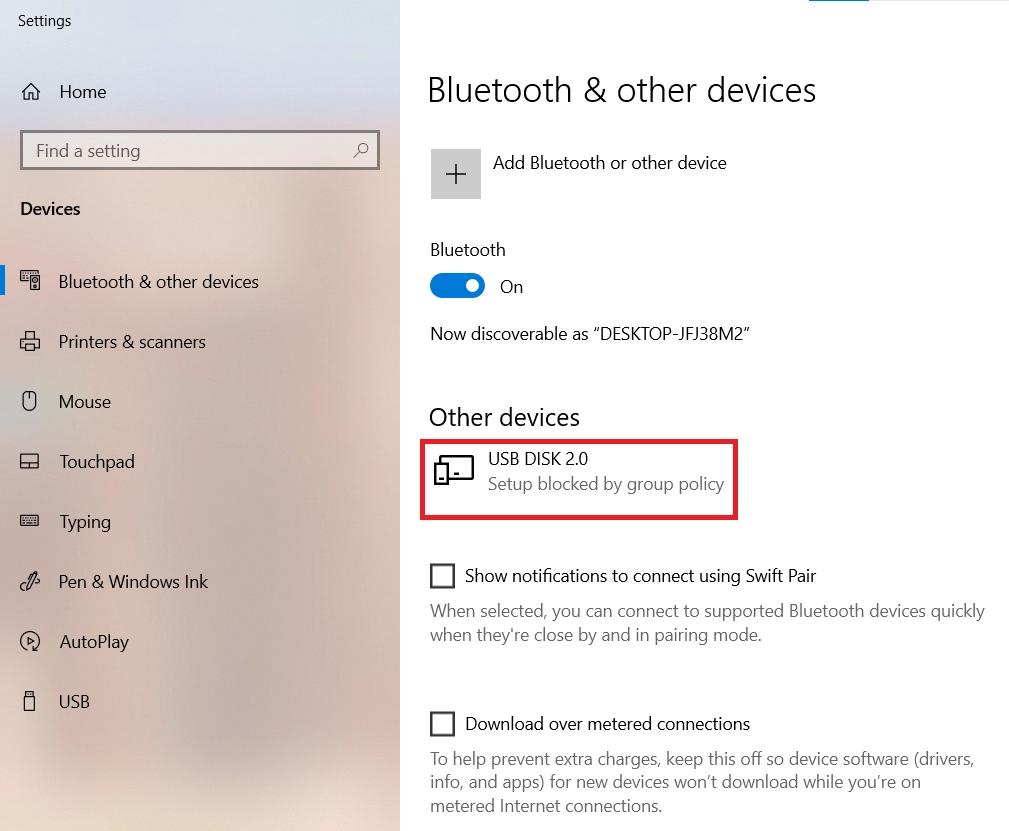
When an unauthorized USB drive is plugged into the managed laptop, Windows detects it under 'Other Devices' but immediately flags it as 'USB DISK 2.0 - Setup blocked by group policy,' confirming that the device was recognized but its installation was prevented by the Intune policy."
Getting the policy live is one thing - making it work in the real world is another. Here are a few simple tips to keep in mind.
Layer Your Security
A USB block works best when paired with other controls. Enforce BitLocker encryption on any allowed drives and consider Microsoft Purview Endpoint DLP to block sensitive file types from being copied - even if USB access is permitted.
Start With a Pilot Group
Don't roll out to everyone on day one. Test with 10 to 20 users first, catch any issues early, then expand gradually.
Tell Users Before You Block
A sudden change with no explanation leads to frustrated employees and helpdesk tickets. Send a quick note explaining what's changing, why, and how they can request an exception if needed.
Audit Before You Enforce
If you're using Defender for Endpoint, run in Audit mode for a few weeks before blocking anything. You'll see exactly how USB drives are being used and can adjust your policy before it causes disruption.
Consider Read-Only Access
Not every organization needs a full block. Allowing read access but denying write access means users can view files from a USB drive but can't copy data onto one - a solid middle ground.
Review Your Policy Regularly
Check your approved device list and policy settings every three to six months. New hardware, staff changes, and Microsoft updates can all affect whether your policy is still doing its job.

Configuring USB blocking policies the right way requires more than just enabling a setting in Intune. It takes the right expertise, a structured approach, and a deep understanding of your environment.
Microsoft Solutions Partner Expertise
As a certified Microsoft Solutions Partner, we bring official Microsoft security guidance together with real-world deployment experience. We ensure your USB device control policies are configured correctly and integrated into your broader endpoint security strategy.
Intune and Defender for Endpoint Specialists
Our team specializes in:
We balance strong security with minimal disruption to your day-to-day operations.
Compliance-Aligned USB Security
We design USB control strategies that support GDPR, HIPAA, PCI DSS, ISO 27001, and SOC 2 requirements by ensuring:
Practical, Real-World Experience
We've helped organizations prevent insider data theft, block USB-based malware, and meet regulatory requirements - across both cloud-only and hybrid environments. Our approach ensures policies work effectively without creating unnecessary friction for end users.
Ready to secure your endpoints the right way?
Schedule a consultation to build the right USB device control strategy for your organization.

Go to Intune Admin Center > Devices > Configuration Profiles > Create Profile. Select Windows 10 and later, choose Settings Catalog, and search for Removable Storage. Enable "Deny Read Access" and "Deny Write Access" and assign it to your target device group. That's it.
Yes. The policies in this guide target removable storage device classes only. Keyboards and mice use a different class called HID (Human Interface Devices) and won't be affected as long as your policy is scoped correctly.
Method 2 gives you much more precise control.
In Intune, go to Device Restrictions for Android devices and toggle off "USB debugging." This prevents users from enabling developer-level USB access on managed Android devices.
Go to Intune Admin Center > Devices > All Devices, select the device, and choose "Block." This prevents the device from accessing corporate resources until it's unblocked or wiped.
Select the device in Intune Admin Center > Devices > All Devices and click "Remote Lock." This immediately locks the screen and requires a PIN to regain access - useful for lost or unattended devices.
Create a Compliance Policy in Intune that marks jailbroken or rooted devices as non-compliant. Pair it with a Conditional Access policy to block those devices from accessing corporate apps and data automatically.
You can use Group Policy on domain-joined devices - navigate to Computer Configuration > Administrative Templates > System > Removable Storage Access and enable "Deny All Access." Alternatively, change the USBSTOR registry key value to 4. Both methods work but lack central monitoring.
Yes. You can enforce BitLocker encryption on USB drives through Intune, which effectively locks the contents behind a password or recovery key. Any unencrypted drive will be blocked from being written to.
It can. Intune's Removable Storage settings include separate rules for optical drives and SD cards. If you enable "All Removable Storage - Deny All Access," it covers those too. Configure based on what your organization actually needs to restrict.
They'll see a standard Windows message - "Location is not available - Access is denied." There's no custom Intune notification explaining the block, so communicating the change to users beforehand is important.
Yes. Enable "Deny Write Access" but leave read access open. Users can view files from a USB drive but cannot copy anything onto it - a good middle ground for organizations that need some USB flexibility.
Yes. Since policies are cloud-delivered through Intune, they apply to any enrolled device regardless of location - office, home, or anywhere else with an internet connection.
For Macs - Defender for Endpoint Plan 2 supports USB device control on macOS. For mobile devices - USB mass storage isn't a typical concern on iOS or Android. Use MDM and MAM policies to control data sharing on mobile instead.
No. Office 365 alone doesn't include device management. You'll need a plan that includes Intune - such as Microsoft 365 Business Premium, E3, or E5 - for centralized USB control.
No. These policies work at the OS level and are extremely lightweight. End users won't notice any difference in device speed or performance.
For Method 1 - check policy status in Intune Admin Center under Devices > Configuration Profiles. For Method 2 - check the Device Control report in the Microsoft 365 Defender portal for blocked events and detailed USB activity logs.
Block all unauthorized USB storage devices using the methods in this guide. Pair that with Microsoft Defender Antivirus, which scans removable media automatically when connected, adding another layer of protection against USB-based malware.
Not on its own. Users could still exfiltrate data through email or cloud storage. Combine USB blocking with Microsoft Purview Endpoint DLP and Conditional Access policies for a complete data loss prevention strategy.
Yes. In Defender for Endpoint, set your Device Control policy to Audit mode. This logs all USB activity without enforcing a block - giving you visibility into usage patterns before you commit to a full restriction.

CEO at Penthara Technologies
 Set Up Device Enrollment in Microsoft Intune – The Right Way - 2026 Guide
Set Up Device Enrollment in Microsoft Intune – The Right Way - 2026 Guide
Learn how to set up Microsoft Intune device enrollment, choose the right method for Windows, iOS, Android, and macOS, and avoid common setup mistakes.
 Microsoft Entra ID Smart Lockout: Prevent Brute-Force Password Attacks
Microsoft Entra ID Smart Lockout: Prevent Brute-Force Password Attacks
Learn how Microsoft Entra ID Smart Lockout works, when to configure it, and best practices to prevent brute-force and password spray attacks.
 Full Wipe vs Selective Wipe in Intune: What IT Admins Need to Know
Full Wipe vs Selective Wipe in Intune: What IT Admins Need to Know
Learn how Intune full wipe and selective wipe work, when to use them, and best practices for secure device management in BYOD and corporate environments.